Spoofed HealthCare Spreads Virus
Blog
Thought Leadership
Spoofed HealthCare Spreads Virus
Fred Touchette
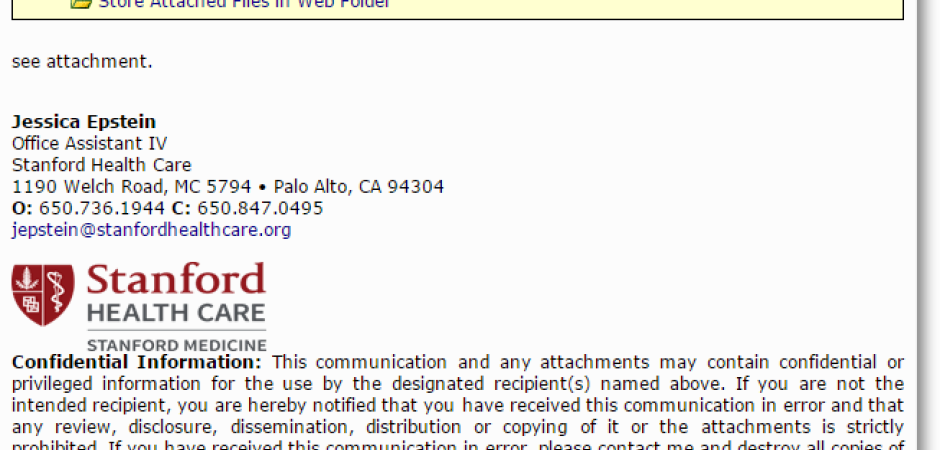
Emails purporting to come from Stanford Health Care deliver malware inside an attachment entitled Customer_department_offer.zip. These emails will use one of six different subject lines in their attempts to trick recipients into fall prey to their campaign. They include: "Special offer", "Health Care", "Thank You", "Important", "check out", and my favorite "Stanford Medecine"[sic]. I enjoy the fact that this particular subject line misspells the word "medicine" especially considering the proper spelling is right there in the graphic they used to spoof Stanford to begin with, but I digress.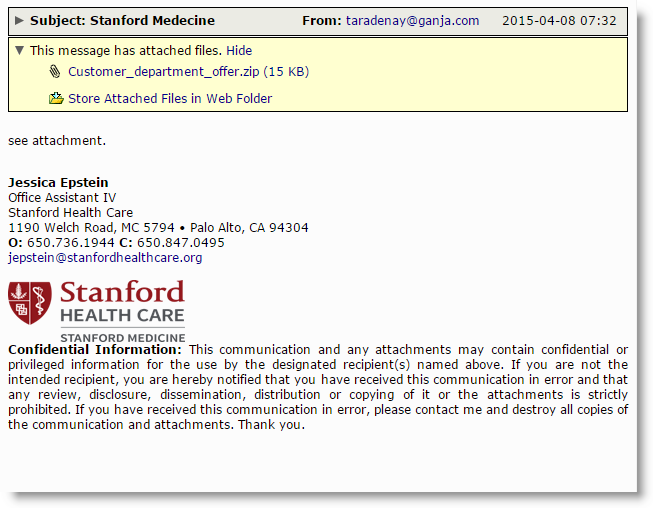
This campaign is directly related to similar campaigns that we have been seeing on a daily basis that usually begin in the mornings as people in the US are getting into work, usually around 6am cst and last for just over an hour delivering right around 1 million pieces. The functionality in these campaigns is the same, as is the fake pdf icon attached to the zipped up executable. The main difference between them is the entity in which they decide to spoof and the contact domains and IPs that the malware attempts to reach out to. This particular campaign reaches out to the domain estelareventos.com as well as an IP in Ukraine 141.105.141.87 on port 13912.
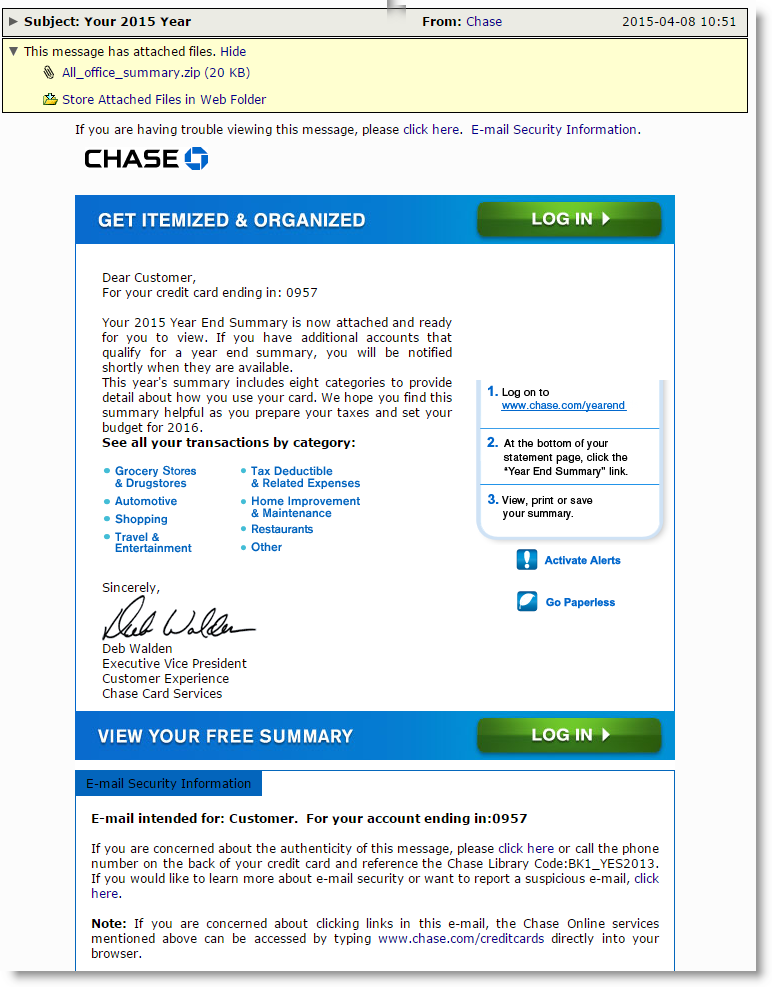
This just in, as I was writing this post the same group began sending yet another campaign, this time impersonating Chase bank which they have been keen to do. This time the malware attempts to connect to sncielles.de, restaurantesdeasturias.com, and 141.105.141.87 again, this time on port 13923.