More Malicious Macros Impersonate UK Winery
Blog
Thought Leadership
More Malicious Macros Impersonate UK Winery
Fred Touchette
Another day, another slew of custom crafted MS Word documents with macro functionality hits our filters. Macros used to be a tool of convenience for Microsoft documents such as Word and Excel, but now they're primarily used for internet evil, so much so that Microsoft has had them disabled by default for years now. The only reason they haven't gone away completely is because some companies are still using them despite their very inherit dangers, likely in legacy documents that have continued to be reused over and over within an organization.
Today's attack began early around 4am cst and continued for the next four hours targeting the inboxes of those just heading into work in the US, though the attacks did not appear to be limited to mailboxes in the United States. By the time this campaign finished up, we had blocked over a half a million pieces associated with this attack.
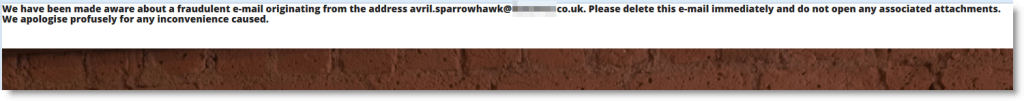
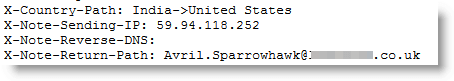
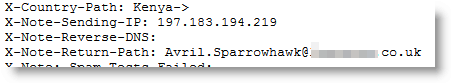
This attack spoofed a winery just outside of London and thanked the recipient for their recent payment, but stated that an invoice had been overlooked. The email was spoofed to look like it was sent by someone from the winery's domain. Even the winery itself placed a warning on their site about the attack saying that these emails originated from the address in question, however, in actuality the address was simply spoofed and originated from a botnet sent out from all over the world. The rest of the email was also well crafted, looking as close to a real correspondence as one can likely get, additionally including footer graphics promoting an actual upcoming event by the winery being spoofed.
The supposed invoice was an attachment by the name of CWIH8974.doc. This was a real MS Word document, although if it were opened, it appeared to have no content. Underneath the surface, though, a macro runs that calls out to the domain powerstarthosting.com where it downloads and executes the file b4387kfd.exe. The newly downloaded executable then reaches out to 92.48.69.11 to get further instructions and payloads.
This campaign is very similar to a campaign we saw a couple of weeks ago where the exact same template was being used to push an attachment by the same name. In this campaign though, the malicious payload was hosted elsewhere - secure.novatronica.com and had a different name - 87t5fv.exe, its intent was the same though, to steal personal information from its victims.
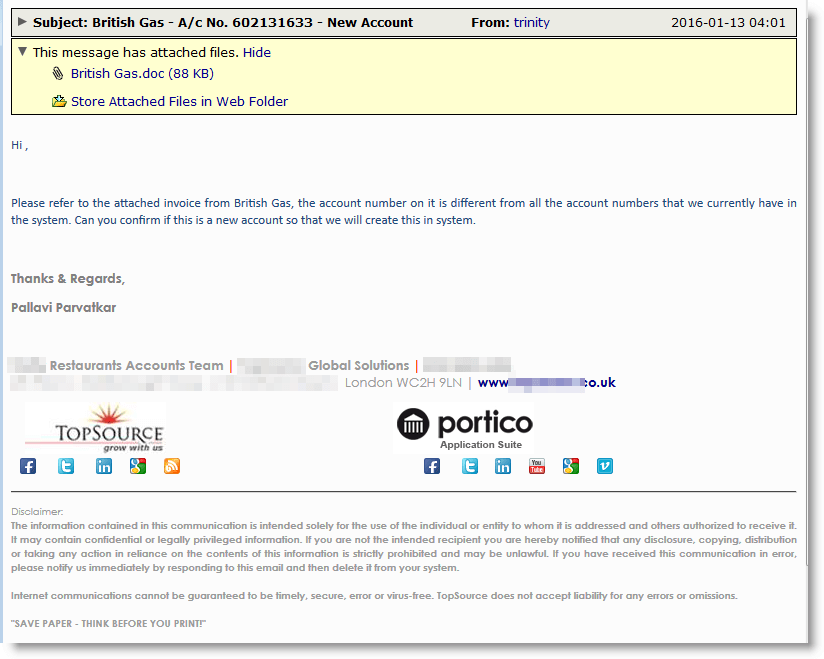
This attack has also used a second theme in order to push its agenda, spoofing another European firm that handles accounting for restaurants in the UK. This time the attachment was entitled "British Gas.doc" and was a supposed bill from the utility company. In this version the malware reaches out to webdesignoshawa.ca and the IP 184.168.192.41 for its payload.
The best way to avoid these attacks is to avoid using macros and leave them disabled. If your company has to use them, I recommend specific user awareness training on how to spot these bad documents and establish procedures for handling possible infections and when you're done with that, go ahead and stop using them.